Get Microsoft Azure Access Token using Postman. The OAuth token contains claims that you can use in Azure AD to identify the granted permissions to APIs. This is part 2 of the series “Create Azure Resource Manager Bot“.
An access token contains claims that you can use in Azure Active Directory B2C (Azure AD B2C) to identify the granted permissions to your APIs. When calling a resource server, an access token must be present in the HTTP request. An access token is denoted as access_token in the responses from Azure AD B2C.
For more information. Refer to Microsoft Documentation.
If you are looking for getting the Azure Access Token for Microsoft Graph API, refer to my post on How to get Azure Access Token using Postman for Microsoft Graph API.
Pre-requisites
- Download Postman
- Service Principal in Azure – To know how to create a service principal, go through my post on Creating Service Principal using PowerShell.
Video
Import Postman Collection
Getting Access Token
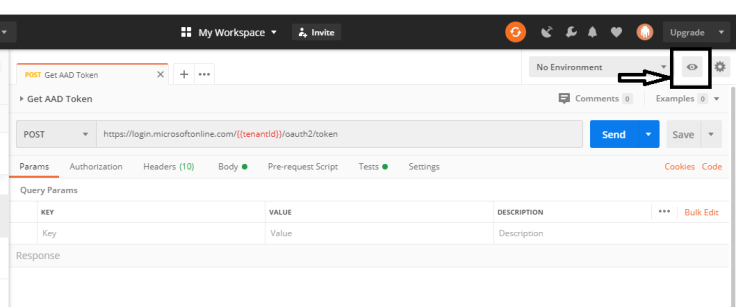
After you create Service Principal, make a note of Tenant ID, Client ID, Subscription ID, and Client Secret. Click on Environment Quick look in Postman
Click on Add new Environment.

Enter Environment name and following variables: tenantId, clientId, clientSecret, resource, subscriptionId.
Give the required values based on your Azure subscription and Service Principal. Give resource as https://management.azure.com/. Scroll down and Update.
The resource varies based on what services and resources you want to authenticate to get the access token. This is specifically for Azure Resource Manager.

Select the created environment from the dropdown.

Send the Post request to get the Access Token in the response.

Thank you All!!! Hope you find this useful.
If you liked our content and it was helpful, you can buy us a coffee or a pizza. Thank you so much.



