Most people’s daily activities include accessing websites or portals. A session is formed every time you log in to one of these websites. A session is defined as the communication between two systems in the simplest possible method. This will be in effect until the user terminates the conversation. A user-initiated session is what this is called.
Any communication that takes place via the internet requires the start of a session. However, the chances of a hijacking session remain. This article will explain what seizures are, how they can occur, and what can be done to prevent them.
What exactly is a hijacking session, and how does it function?
The hijacking of the session is exactly what it sounds like. The user’s session can be hijacked by the attacker, leaving him unable to control the time and his personal data to be captured. An attacker can steal user time once it has started, such as by logging into a financial website.

To time off, the attacker must have a good understanding of the user’s cookie session. Although each session can be hijacked, browser times on online applications are the most common.
What causes a session to be hijacked?
Depending on the location of the attacker and the vector, the attacker can hijack the user’s time in various ways. Here are a few examples of how a session can be hacked:
Cross-site scripting (XSS): Attackers take advantage of bugs on servers or programs to inject Java text into client clients’ web pages, allowing your browser to use incorrect code when the page is loaded. Injectable scripts can gain access to your session key if the server does not specify HTTP Only for session cookies, giving attackers the information they need to interrupt your session.

Session-side jacking: An attacker can monitor network traffic and hold user time cookies once they have been verified using packet sniffing. If a website only uses SSL / TLS encryption on its login pages, the attacker can hijack the user’s time and impersonate them to perform web applications using the session key they found in packet sniffing. This is most common when an unprotected WiFi Hotspot is used to gain network access, monitor traffic, and set up their access points to attack.

Session fixation: Attackers provide a session key and trick the user into accessing a compromised server using this method.

Due to the unfounded protocol, there is a risk of session hijacking. These protocols are flawed, making them vulnerable to attack.
Encryption Function
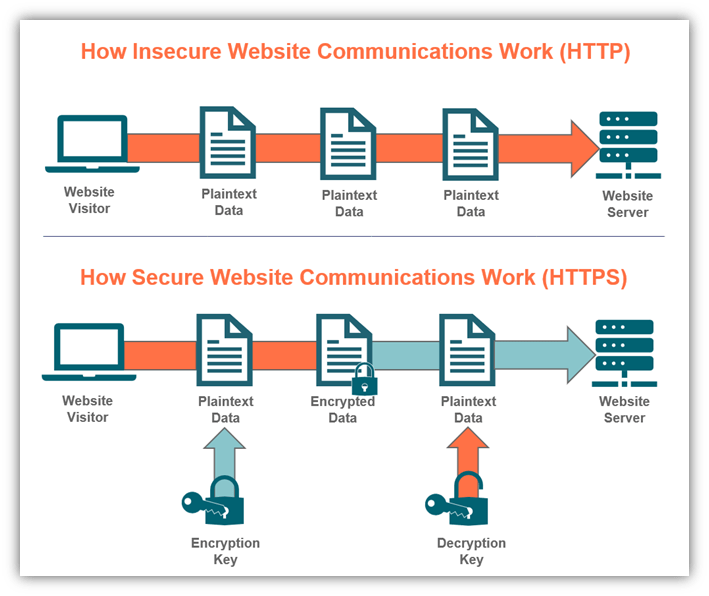
Organizations can use encryption to protect user time from theft. This encryption, which comes in the form of certificates, is required to protect your clients’ time.
SSL: SSL stands for Secure Sockets Layer, and is the industry standard for keeping secure Internet connections and protecting any sensitive data transmitted between two systems, preventing thieves from reading and modifying any information provided, including potentially personal information.

TLS: TLS (Transport Layer Security) is a more secure version of SSL-enhanced.

Hijacking Session is an example of a hijacking session
Data breach in the congestion rate of TLS applications using session attacks. This allows them to access users ‘login cookies, which they can use to hijack users’ time. In September 2012, CRIME, a team of session hijackers, hacked into the company’s website.
By removing the HTTPS cookies set by the website, CRIME was able to hijack time and use malicious power to authenticate itself as users, symbolizing large amounts of data.
How Can You Protect Yourself From Hijacking?
You should increase the protection of online programs to protect yourself from hijacking while you are in session. Communication and session management can help with this. There are a few things you can do to reduce your chances of having your session hijacked:
HTTPS: The use of HTTPS ensures that all session traffic is encrypted with SSL / TLS. Even if the victim’s traffic is monitored, the attackers will not be able to block the session ID of the blank text. To provide complete encryption, HSTS (HTTP Strict Transport Security) is recommended.
HTTPOnly: Using the HTTPOnly site prevents client scripts from accessing stored cookies. This can help prevent XSS attacks that are based on adding Java Scripts to web pages.
System Updates: Update your system with reliable antivirus software that can quickly detect viruses and protect you from all kinds of malware (including malware attackers that they use to commit session robberies). Set automatic updates to all your devices to keep your systems up-to-date.
Session Management: Instead of creating their own session management solutions, website administrators can use web frameworks to provide acceptable security.
Time Key: After initial authentication, it is a good idea to reproduce session keys. As a result, attackers’ time IDs mean nothing because ID changes immediately after verification.
Identity Verification: Do some personal verification from the user in addition to the session key. Checking a common user IP address or application usage patterns is one example.
Public Hotspot: To protect the integrity of your times, avoid using public WiFi and instead use encrypted wireless networks.
VPN: To protect yourself from hackers, use Virtual Private Network (VPN). By creating a “private tunnel” where all your online activities are recorded, a VPN closes your IP address and keeps your session secure.

Fraud: How to Survive a Fraud Aft Focus Click only the links in the emails that you have verified from the official sender.
Conclusion
The hijacking of the session is a major concern, as users are always at risk of being hacked. By applying security measures, website administrators can limit these risks in a number of ways. Deep encryption on all web applications is used in these security measures to block all attackers’ access points to disrupt user time.



Leave a Reply